How To Manually Remove Malware From Websites
Your website has been compromised, and you suspect the attackers have injected malware into its code. What can you do about it? There are many ways to approach a malware infection, and we’ll look at some in a moment, but your final recourse may be to roll up your sleeves, hunt through the site’s files, and remove the malware manually.
This article will show you how to find malware code in your site’s files and remove it, using a WordPress site as an example. You don’t have to be a developer to follow along, but you’ll be better able to identify malware if you have some familiarity with coding and the language the site is written in; PHP in WordPress’s case.
How To Avoid Manually Removing Malware from Websites
In an ideal world, you wouldn’t have to remove malware manually. It can be a tedious process, especially if you can’t distinguish between malware and innocent code your site relies on. It’s also easy to miss malware code—online criminals are sneaky, and they go to great lengths to hide it. Unfortunately, you might spend hours hunting down and deleting malware traces, only for a hidden backdoor to reinfect the site immediately.
The best option is to avoid malware infection in the first place. Make sure your site is updated, and turn on automatic updates if possible. Be careful when installing plugins and themes, and avoid nulled or pirate software at all costs; it is invariably loaded with malicious code.
Automatic malware detection and removal is also less demanding than manual malware removal. cPanel & WHM supports the excellent free ImmunifyAV scanner, which you can install via WHM’s Security Center. It alerts you when it finds a suspected malware infection and tells you where it is. If you upgrade to ImunifyAV+, you’ll be able to remove malware with the click of a button too.
Finally, if you suspect an infection, you should attempt to restore a recent clean backup. Restoring from an uninfected backup overwrites malicious files with clean originals. cPanel’s WordPress Toolkit makes it easy to back up WordPress sites in seconds, or you could use one of the many WordPress plugins that offer backup functionality.
If you don’t have a recent backup, then you’ll have to dig in and replace infected files manually.
Manually Removing Malware from a WordPress Site
We’re using WordPress in our walkthrough because it’s the most popular CMS, but a similar process works just as well on other content management systems and ecommerce stores.
It should be mentioned that we’re making a big assumption in this article. We’re hoping the malicious code is limited to your website and that the attacker hasn’t gained access to your web hosting server. However, if the server is compromised, the attacker may have replaced system binaries with rootkits and other malware. If that’s happened, you can’t trust any software on the server, including the software we’re about to use to clean malicious code from the site.
Before tackling malware removal on WordPress, you should:
- Take the site offline. If possible, use WordPress Toolkit’s maintenance mode to avoid exposing users to further risk.
- Make a backup. Back up your site whenever you make changes to its code or database.
- Turn on debug settings. Debug settings allow WordPress to print error messages to the screen. They’ll help you to figure out what went wrong if you make changes that break the site. You can read more about debug settings and maintenance mode in WordPress® Debugging with cPanel and WordPress Toolkit.
First, we’ll check to see if any files have been modified in the last few days. Most WordPress files are not frequently modified except for static assets like images, so recent changes are a helpful clue.
Log in to your server via SSH or open the cPanel Terminal and navigate to the infected site’s directory. You’ll find the Terminal under Advanced in the cPanel main page menu. Your WordPress site is most likely in public_html or a directory inside public_html.
Run the following command:
find . -name '*.ph*' -mtime -7This displays a list of all PHP files modified in the last seven days. WordPress has hundreds of files that might hide malware, but let’s assume that wp-config.php is at the top of your list. Next, we need to look inside to see if there is any sign of malicious code.
Open the file in your text editor. If you prefer not to work with command-line text editors, locate the file in cPanel’s File Manager, and click Edit in the menu bar. You’re looking for anything that seems out of place.
Keep an eye out for these red flags:
- Mismatched coding styles — the lines of code may be longer, improperly indented, or excessively complex.
- Obfuscated code — code that has been deliberately disguised. It looks like long strings of meaningless letters and numbers. Not all code that looks like this is malicious; you may come across legitimate hashes that match this description, especially in configuration files.
- Strange URLs — most URLs in your site’s files are related to the site itself. If you see an unusually formatted or excessively long web address, it may link to a server under the attacker’s control.
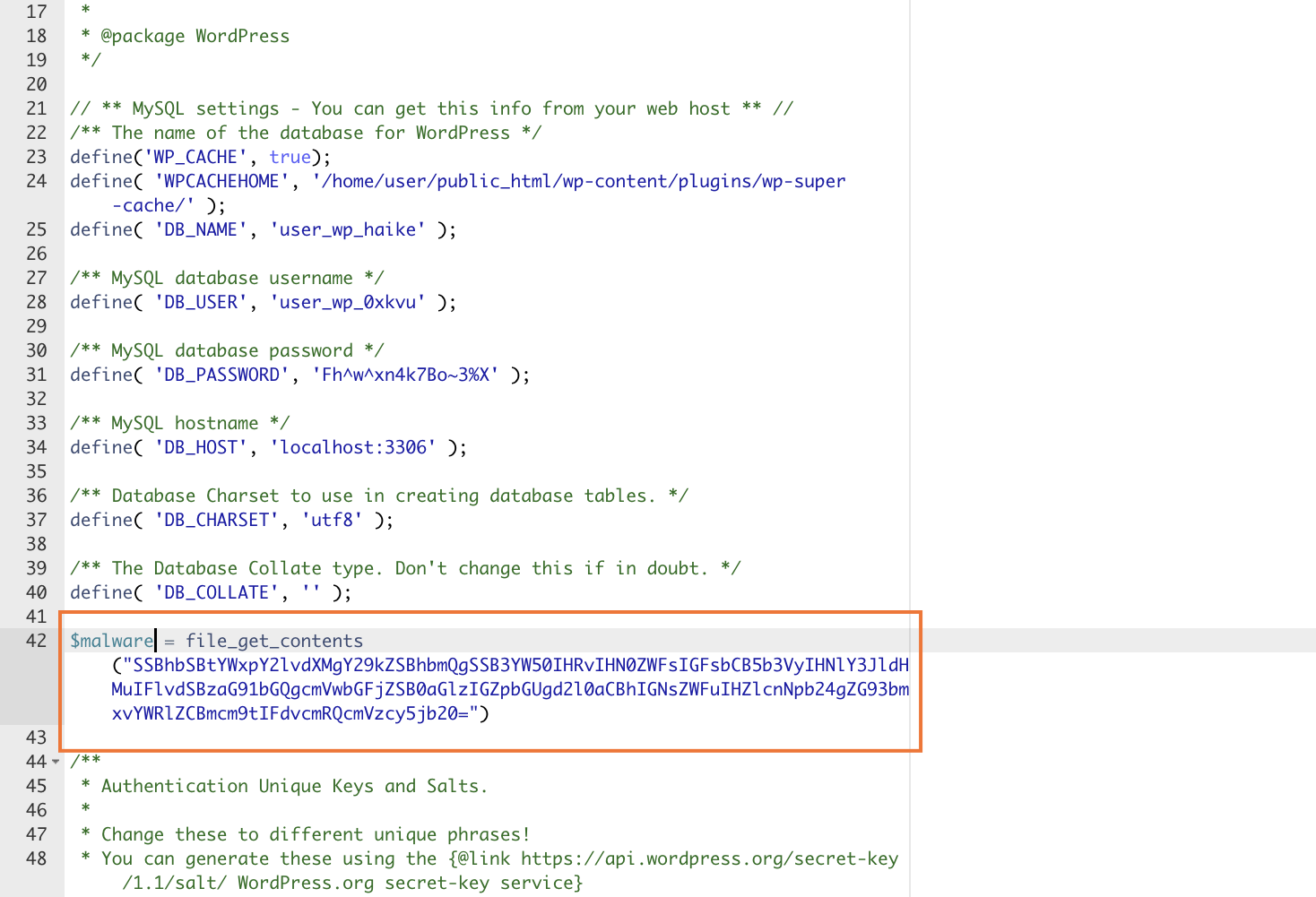
For example, if you see something like this mixed in with the familiar PHP code, it’s almost certainly malware.
Most malicious code isn’t that obvious. However, you can compare files with the original to see if anything looks out of place. Download a fresh copy of the same version of WordPress from WordPress.org. If a plugin or theme file is under suspicion, download a new version from the developer’s site or the WordPress repository.
Open your newly downloaded version and compare it to your site’s file. They may not be identical, but you should view any significant differences with suspicion.
In many cases, you can simply replace an infected file. Manually clearing malware is a careful process of exchanging infected files for uninfected originals. However, you must be careful not to simply replace files that contain essential configuration data. For example, if you swap wp-config.php for a freshly downloaded file, your site will stop working because that file contains site and database configurations.
If you aren’t sure what a file does, check the WordPress documentation to ensure that it is safe to exchange. You may have to copy information from the infected file to its replacement, making sure no malicious code makes its way across.
To replace files, use cPanel’s File Manager to delete the infected original and upload the replacement. Then, verify the site still works every time you make a change. If you don’t regularly check and only notice the problem later, you may have no idea which edit did the damage.
As we mentioned at the beginning of this article, manual malware removal is a long and tedious process. And there is no guarantee that you’ll find all the malicious code. However, it’s a valuable technique to have under your belt when automatic malware removal and back-ups let you down. As always, if you have any feedback or comments, please let us know. We are here to help in the best ways we can. You’ll find us on Discord, the cPanel forums, and Reddit. Be sure to also follow us on Facebook, Instagram, and Twitter.